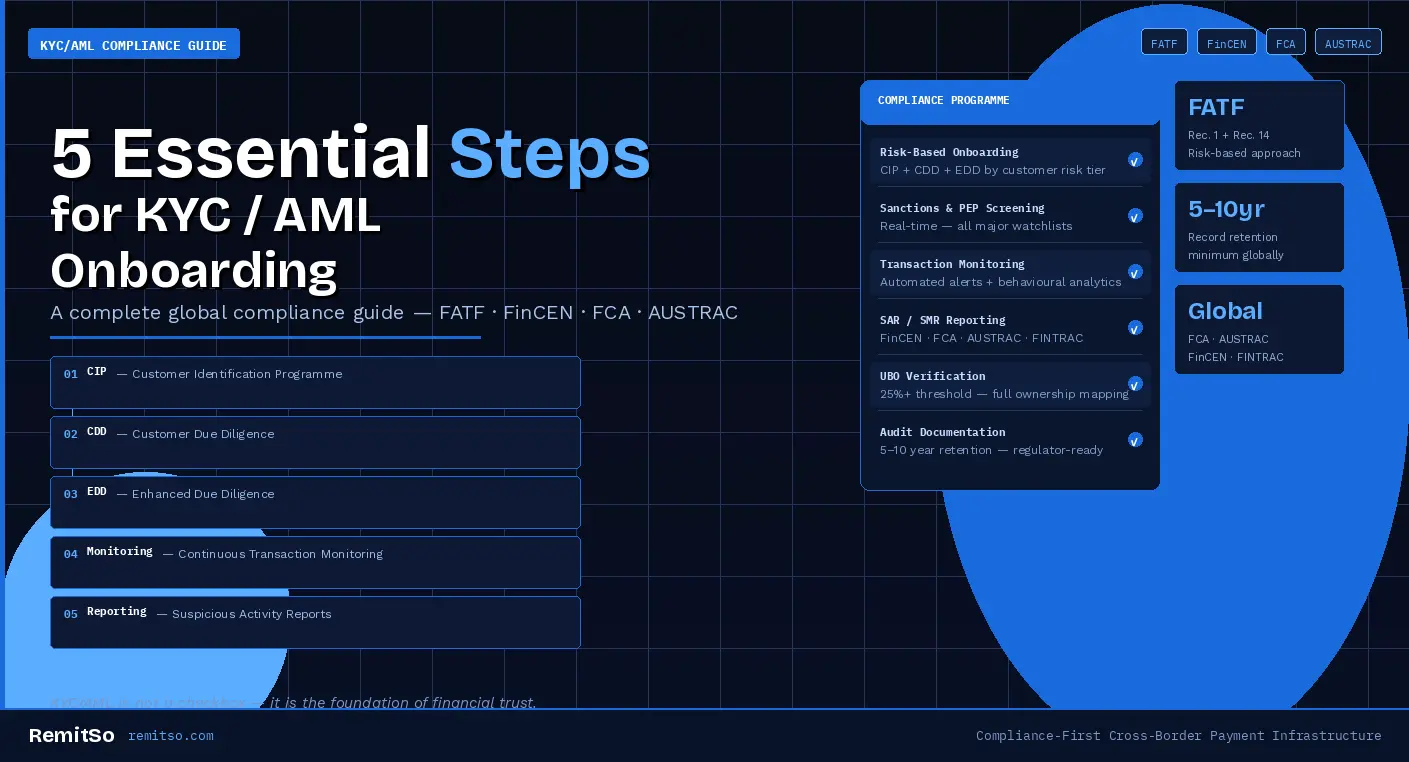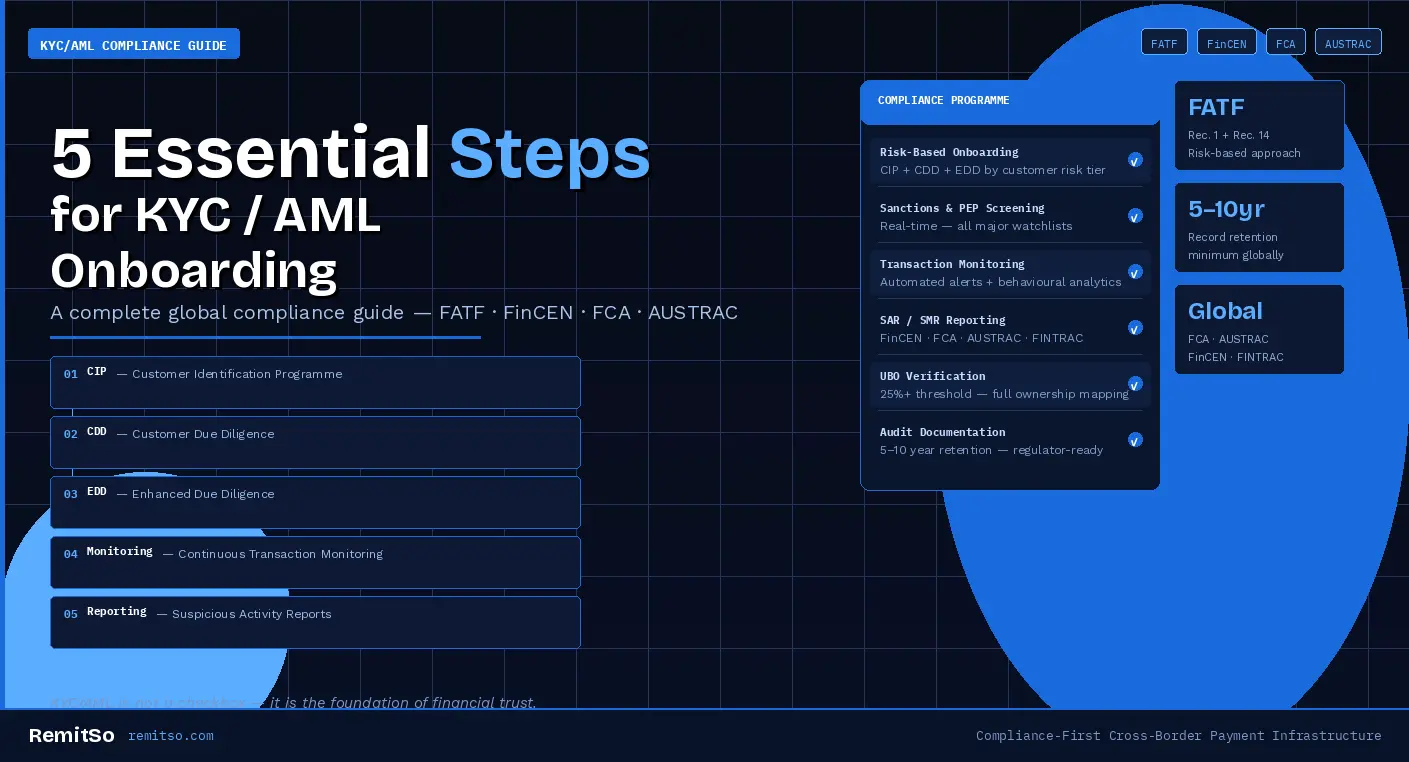
Financial crime is evolving rapidly — and regulatory scrutiny is intensifying across jurisdictions. Financial institutions, remittance providers, fintech platforms, payment processors, and digital financial services businesses are now expected to operate highly structured, risk-based compliance programmes. KYC (Know Your Customer) and AML (Anti-Money Laundering) compliance are no longer administrative obligations. They are foundational to operational integrity, regulatory trust, and long-term growth. This guide explains the five essential steps of modern KYC/AML onboarding — from Customer Identification Programmes to continuous monitoring and regulatory reporting — aligned with global standards including FATF, FinCEN, the FCA, AUSTRAC, and EU AML Directives.
In This Article
KYC and AML frameworks exist to protect the global financial system from identity fraud, money laundering, terrorist financing, sanctions evasion, corruption, synthetic identity abuse, and illicit cross-border flows. For remittance and cross-border payment businesses in particular, compliance standards are especially stringent due to the nature of international fund flows — multiple jurisdictions, multiple currencies, and multiple regulatory frameworks intersect in every transaction corridor.
Failure to implement robust compliance measures can result in significant regulatory penalties, licence restrictions or revocation, loss of correspondent banking relationships, severe reputational damage, and personal liability for senior management. These consequences are not theoretical. Regulators including the FCA, FinCEN, AUSTRAC, and the EU's AML supervisory authorities have demonstrated consistent willingness to pursue enforcement actions against operators whose compliance programmes are inadequate — regardless of whether actual financial crime was facilitated.
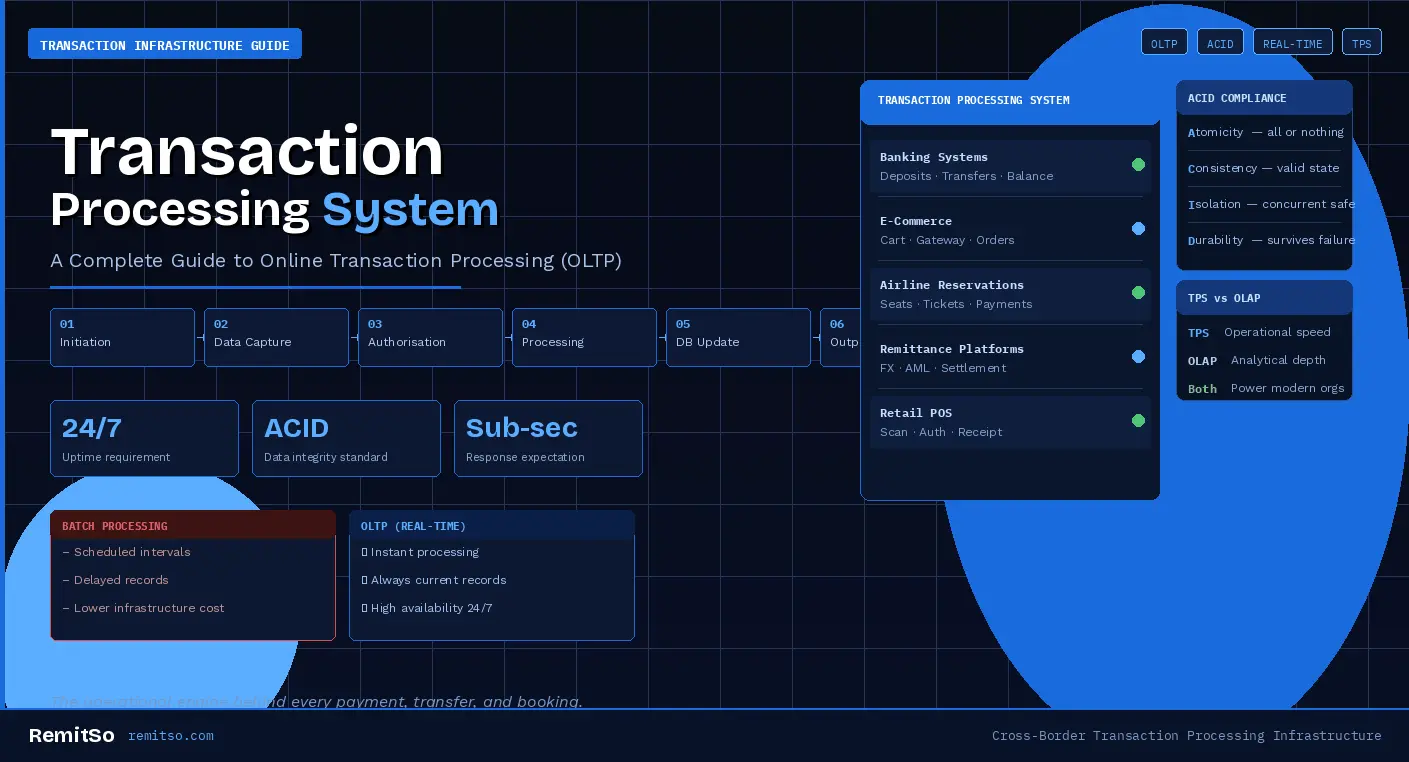
Figure 1: Four minimum standards regulators now expect as baseline compliance — not aspirational targets
The Customer Identification Programme is the foundation of KYC compliance. Its purpose is to verify that every individual or entity onboarding is genuinely who they claim to be — establishing identity with sufficient certainty to support the risk assessment that all subsequent compliance steps depend on. Under regulations including the UK Money Laundering Regulations, the US Bank Secrecy Act, and EU AML Directives, institutions must collect and verify specific identity data before establishing a customer relationship.
For individuals, CIP requires the collection and verification of full legal name, residential address, date of birth, government-issued ID number, and tax identification number where applicable. For businesses, the requirements extend to the legal entity name, incorporation documentation, business registration number, registered address, Ultimate Beneficial Owners, and directors and controlling persons. The corporate CIP is typically more complex than the individual equivalent because ownership structures can be multi-layered — and the obligation is to trace them through to the natural persons who ultimately own or control the entity.
Figure 2: CIP data and verification requirements for individual vs business customers under global AML standards
CIP establishes the baseline risk profile and ensures that only verified customers enter the financial ecosystem. The verification process must satisfy the reliability and independence standard — meaning that the documents or data used to verify identity must come from sources that are independent of the customer themselves. Electronic verification via trusted government databases, such as the UK's document verification services or the US NIDPF, is increasingly recognised as meeting this standard while providing a frictionless customer experience.
Customer Due Diligence assesses the risk level of a verified customer. While CIP establishes who the customer is, CDD determines what risk they represent — and therefore what level of ongoing scrutiny the relationship requires. CDD examines the intended nature of the relationship, expected transaction volumes and patterns, geographic exposure, source of funds where required, and the customer's industry and business model risk profile.
Global standards, particularly FATF Recommendation 1, require institutions to apply a risk-based approach that is proportionate to the actual risk the customer presents. Low-risk customers may qualify for Simplified Due Diligence — a lighter documentation and verification burden. Medium-risk customers undergo Standard CDD, which captures the full suite of relationship information. High-risk customers require Enhanced Due Diligence, which goes beyond standard data collection to investigate source of wealth, senior management approval, and additional documentation. CDD enables compliance teams to build defensible customer risk profiles and detect inconsistencies before financial exposure increases.
| Risk Level | Due Diligence Type | Key Requirements |
|---|---|---|
| Low Risk | Simplified Due Diligence (SDD) | Reduced documentation burden — periodic review, basic transaction monitoring |
| Medium Risk | Standard Customer Due Diligence | Full CIP + relationship purpose + expected transaction profile + source of funds |
| High Risk | Enhanced Due Diligence (EDD) | All standard CDD + source of wealth + senior management approval + increased monitoring frequency |
Figure 3: Risk-based due diligence levels and minimum requirements under FATF Recommendation 1
Enhanced Due Diligence is required when elevated risk indicators are identified — either at onboarding or at any point during the customer lifecycle when risk factors change. EDD is not a higher-intensity version of standard CDD. It is a qualitatively different investigation that goes beyond verifying who the customer is and assessing their declared risk profile, to actively investigating whether the relationship presents ML/TF risk that cannot be adequately managed through standard controls.
EDD commonly applies to Politically Exposed Persons, customers from sanctioned or high-risk jurisdictions as designated by FATF, customers with complex corporate ownership structures, customers in high-risk sectors including cryptocurrency, gambling, and cross-border trade, and clients linked to adverse media. With financial criminals increasingly using shell entities, synthetic identities, and nominee structures to obscure beneficial ownership, EDD has become one of the most operationally critical stages of the compliance lifecycle.
Figure 4: Four primary EDD triggers and the specific investigation requirements each activates
KYC does not end at onboarding. AML compliance requires ongoing monitoring of customer behaviour across the entire lifecycle of the relationship — because financial crime patterns often emerge after a relationship is established, not at the point of initial onboarding. A customer who passes CIP and CDD at onboarding may subsequently exhibit transaction behaviour that is inconsistent with their declared risk profile, indicating either that the initial assessment was incomplete or that the customer's activities have changed.
Continuous monitoring is designed to detect unusual transaction volumes, rapid fund movements, structuring or smurfing activity — where transactions are broken into smaller amounts to avoid reporting thresholds — sudden behavioural changes, exposure to newly sanctioned entities, and updated PEP or watchlist matches. Modern AML frameworks rely on real-time transaction monitoring systems, automated alert engines, behavioural analytics that identify deviation from established customer patterns, and periodic rescreening against sanctions and PEP databases.
| Risk Signal | What It May Indicate | Monitoring Mechanism |
|---|---|---|
| Unusual transaction volumes | Layering, proceeds of crime entering system | Rule-based volume thresholds + velocity checks |
| Rapid fund movements | Integration phase of laundering cycle | Time-series analysis, funds-in-transit flags |
| Structuring activity | Deliberate evasion of reporting thresholds | Pattern recognition across transaction sequences |
| Sudden behavioural change | Account compromise or new illicit use | Deviation from established customer behaviour baseline |
| New sanctions / PEP match | Customer risk profile has materially changed | Real-time rescreening against current watchlists |
Figure 5: Five key continuous monitoring risk signals, their AML implications, and the detection mechanisms required
Continuous oversight is particularly important for remittance and cross-border operations, where transaction patterns can change rapidly, customer corridors shift with geopolitical developments, and the regulatory risk environment in destination jurisdictions evolves continuously. A monitoring framework that was calibrated to a customer's transaction profile six months ago may no longer be appropriate if that customer has expanded into new corridors or significantly increased transaction volume. Monitoring rules must be reviewed and recalibrated regularly — not simply deployed at onboarding and left static.
When suspicious activity is identified through transaction monitoring or customer due diligence, institutions must file formal reports with relevant authorities. The legal obligation to report is not conditional on certainty — a suspicion is sufficient and legally required to trigger a report. Filing late, or failing to file when a suspicion exists, is itself a compliance breach that can attract significant regulatory sanction independently of the underlying financial crime.
Suspicious Activity Reports are filed with FinCEN in the United States, the FCA and National Crime Agency in the United Kingdom, AUSTRAC in Australia, FINTRAC in Canada, and Financial Intelligence Units in jurisdictions globally. Each jurisdiction has specific filing timeframes, format requirements, and tipping-off prohibitions that must be strictly observed. The tipping-off prohibition — which prevents the reporting institution from disclosing to the customer that a SAR has been filed — creates particular operational complexity in customer relationship management that compliance teams must be trained to navigate.
| Jurisdiction | Reporting Body | Report Type | Retention Period |
|---|---|---|---|
| United States | FinCEN | SAR (Suspicious Activity Report) | 5 years |
| United Kingdom | FCA / NCA | SAR (Suspicious Activity Report) | 5 years |
| Australia | AUSTRAC | SMR (Suspicious Matter Report) | 7 years |
| Canada | FINTRAC | STR (Suspicious Transaction Report) | 5 years |
| EU Members | National FIU | STR (per national transposition) | 5 years |
Figure 6: Suspicious activity reporting obligations, receiving bodies, and minimum record retention periods across major jurisdictions
Beyond suspicious activity reporting, institutions must maintain comprehensive AML records for the periods required by their operating jurisdictions — typically between five and ten years. These records include identity documents, verification logs, risk assessments, monitoring alerts, SAR submissions, and complete audit trails of compliance decisions. Regulatory examinations increasingly focus on documentation quality and audit readiness — the ability to demonstrate, through records, that the compliance programme operated as documented and that every decision was defensible at the time it was made.
Financial crime methodologies continue to evolve at pace — and compliance programmes that were designed around the threat landscape of three to five years ago may be structurally inadequate for the risks that regulated entities face today. Three categories of emerging risk are reshaping AML compliance requirements across the industry.
Deepfake technology and generative AI have created new categories of identity fraud that traditional document verification and liveness checks were not designed to detect. AI-generated identity documents that pass optical character recognition checks, synthetic biometric profiles that defeat standard liveness detection, and AI-produced corporate documentation that mimics genuine incorporation records are all active threats in the current compliance environment. CIP frameworks that rely solely on document upload and automated OCR are increasingly insufficient — biometric liveness checks with anti-spoofing capabilities, and AI-enhanced document forensics, are becoming baseline requirements rather than premium add-ons.
Geopolitical developments frequently alter sanctions lists and high-risk jurisdiction designations with little advance notice. An operator whose sanctions screening is based on weekly or monthly list updates rather than real-time feeds is structurally exposed to sanctions evasion between update cycles. The OFAC, HM Treasury, and EU sanctions regimes all publish updates that can be triggered by geopolitical events — real-time or near-real-time screening against all relevant sanctions lists is the only defensible approach for cross-border payment operators.
Remittance and international payment providers face heightened scrutiny because they operate across multiple jurisdictions simultaneously — each with its own regulatory framework, reporting obligations, and enforcement posture. Multi-jurisdictional operations require compliance programmes that can accommodate different AML standards without creating gaps at the intersection between them. Technology-enabled compliance infrastructure that maps regulatory requirements by corridor and jurisdiction, and that generates the right documentation for the right authority, is increasingly essential rather than aspirational.
For remittance providers and financial businesses operating across borders, compliance must be seamless, scalable, and regulator-ready. The five-step KYC/AML framework — CIP, CDD, EDD, continuous monitoring, and regulatory reporting — represents significant operational complexity when implemented across multiple jurisdictions, currencies, and customer risk profiles. Building and maintaining this infrastructure manually, or through disconnected point solutions, introduces exactly the fragmentation and documentation gaps that regulators identify as compliance failures.
RemitSo supports modern compliance operations through integrated capabilities covering structured onboarding workflows, identity verification support, sanctions and PEP screening, risk-based due diligence processes, ongoing transaction monitoring, and centralised audit documentation. By unifying onboarding, monitoring, and reporting within a structured operational environment, RemitSo helps financial institutions maintain regulatory alignment while supporting secure, compliant growth. Robust KYC/AML compliance is not simply about avoiding penalties — it is foundational to building the trust, protecting the customers, and enabling the sustainable expansion that regulated markets require.
For individual customers, KYC onboarding typically requires a government-issued photo ID — passport, driver's licence, or national identity card — plus proof of residential address such as a utility bill or bank statement dated within three months. Date of birth and a tax identification number are also collected where required by jurisdiction. For business customers, the requirements extend to incorporation documents, a business registration number, registered address confirmation, identification and verification of all directors and controlling persons, and full Ultimate Beneficial Owner disclosure — tracing through all layers of corporate ownership to the natural persons who own or control 25% or more of the entity.
KYC — Know Your Customer — is the process of verifying the identity of customers before and during the financial relationship. It establishes who the customer is, what risk they represent, and what ongoing monitoring their relationship requires. AML — Anti-Money Laundering — refers to the broader framework of controls, monitoring, and reporting obligations designed to prevent, detect, and report money laundering and terrorist financing. KYC is a component of AML: effective KYC provides the customer identity and risk profile data that makes transaction monitoring, suspicious activity detection, and regulatory reporting possible. Neither is meaningful without the other — KYC without ongoing AML monitoring is incomplete, and AML monitoring without accurate KYC has no reliable baseline against which to measure suspicious behaviour.
Enhanced Due Diligence is triggered by the presence of elevated risk indicators — either at the point of onboarding or at any subsequent point in the customer lifecycle when those indicators emerge. Key triggers include PEP status or close association with a PEP, sanctions exposure or links to sanctioned jurisdictions, high-risk geographic exposure as designated by FATF or national risk assessments, complex or opaque corporate ownership structures that make UBO identification difficult, high-risk sector activity including cryptocurrency, gambling, and certain cross-border trade categories, and adverse media findings linking the customer to financial crime, regulatory action, or reputational risk. EDD is also required when a customer's transaction behaviour is inconsistent with their declared risk profile in a way that cannot be explained by updated standard CDD.
Regulators require continuous or near-continuous rescreening against sanctions and PEP lists — not periodic batch checks. Sanctions lists can be updated at any time in response to geopolitical events, and the obligation to freeze or block a sanctioned customer's assets applies from the moment the designation is made, not from the next scheduled screening cycle. Practically, this means that compliance infrastructure must maintain real-time or near-real-time feeds from all relevant sanctions lists — OFAC, HM Treasury, EU, UN, and any jurisdiction-specific lists applicable to the corridors and markets the business operates in — and apply automated rescreening against those feeds as they are updated. Periodic rescreening for broader risk profile review is typically conducted at minimum annually and whenever a material change in the customer's circumstances or behaviour is identified.
A Suspicious Activity Report is a legally required filing submitted to the relevant Financial Intelligence Unit when a regulated institution knows, suspects, or has reasonable grounds to suspect that a transaction or customer activity involves the proceeds of crime, money laundering, or terrorist financing. The filing obligation is triggered by suspicion — not certainty — and applies regardless of whether the transaction has been completed or prevented. Filing timeframes vary by jurisdiction but are typically between three and thirty days of forming the suspicion. The tipping-off prohibition means the institution cannot inform the customer that a SAR has been filed. Failure to file a SAR when suspicion exists is a standalone criminal offence in most jurisdictions, independent of whether any underlying financial crime occurred.
Yes — remittance and cross-border payment businesses are subject to enhanced regulatory scrutiny because of the nature of international fund flows. The multi-jurisdictional reach of remittance operations means that funds may pass through several regulatory environments in a single transaction, creating multiple points of ML/TF vulnerability. FATF Recommendation 14 specifically addresses money or value transfer services and requires that they be licensed, monitored, and held to AML standards equivalent to those applied to banks. In practice this means that a remittance operator faces compliance obligations in its home jurisdiction, in the destination jurisdictions of its corridors, and through its correspondent and payout partner relationships — each of which has its own regulatory framework and examination posture.
AML record retention requirements vary by jurisdiction but typically range between five and ten years from the end of the customer relationship or the date of the transaction. In the UK and EU, the standard is five years. In Australia, AUSTRAC requires seven years. In some jurisdictions with heightened AML risk assessments, longer retention may be required or expected in practice. Records that must be retained include identity documents and verification logs, all CDD and EDD documentation, risk assessment outcomes and updates, transaction monitoring alerts and the decisions made in response, SAR and SMR filings, and complete audit trails of compliance decisions. Records must be stored securely, be retrievable on request by the competent authority, and maintain their evidentiary integrity for the full retention period.
Yes — and regulators increasingly expect technology-enabled compliance rather than treating it as a premium option. Automated identity verification systems with biometric liveness checks and AI-enhanced document forensics improve both the speed and the accuracy of CIP compared to manual document review. Automated transaction monitoring systems apply consistent rules to every transaction regardless of volume — eliminating the inconsistency that characterises manual review at scale. Real-time sanctions and PEP screening removes the gap between list updates and screening application. Centralised audit documentation platforms ensure that every compliance decision is recorded with the context needed to defend it in examination. The combination of automation and structured oversight allows compliance teams to focus human judgement on genuine exceptions and complex cases — which is precisely where it adds the most value.